Any Data State • Total Data Protection • One Platform
Data
Discovery, Classification, Masking & Monitoring
Platform for the AI-Modern Enterprise
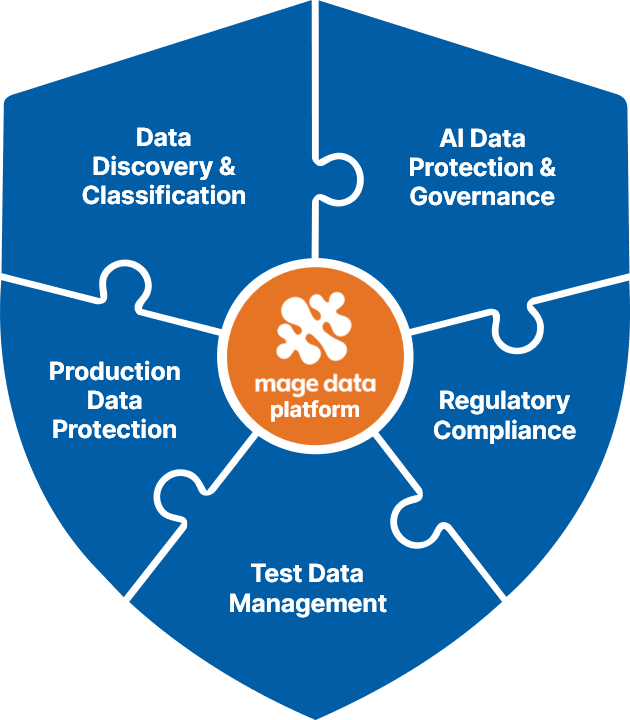
An AI-driven, integrated conversational platform empowering enterprises to automate Data Discovery & Classification, AI Data Protection, Test Data Management, Production Data Protection and Regulatory Compliance from a single pane of glass
Customer Recognition
 Anonymous Customer Reviews
Anonymous Customer Reviews Analyst Recognition

Enterprise Use Cases
Access to Privacy-Compliant Data without the Friction.
One Solution.
From data discovery and classification to AI governance — one integrated solution that removes every barrier between your data and your innovation
Data Discovery & Classification
Discover every sensitive data element across databases, file storage, workstations, and multi-cloud environments. Classify, tag, and catalog data with AI-powered accuracy — then enforce protection policies that bind directly to asset classes for consistent, data-centric security.
Learn moreKey Capabilities
AI Data Protection & Governance
Accelerate AI adoption with enterprise-grade data guardrails. Secure the entire AI/ML lifecycle from data collection to model deployment — block sensitive data from reaching public LLMs with sub-100ms inspection, and prepare privacy-preserving AI-ready datasets at scale.
Learn moreKey Capabilities
Test Data Management
Eliminate data friction and provision secure, high-quality test data in minutes. Combine static masking, intelligent subsetting, and database virtualization to fuel CI/CD pipelines — slashing storage costs by up to 90% while ensuring compliance and referential integrity.
Learn moreKey Capabilities
Production Data Protection
Shield your live production environments with a unified defense-in-depth strategy. Integrate role-based dynamic masking, precision redaction, database firewalls, and activity monitoring — all operating in real-time without degrading application performance.
Learn moreKey Capabilities
Regulatory Compliance
Navigate the complex global regulatory landscape with purpose-built compliance capabilities. Pre-built policies for GDPR, HIPAA, DPDP, PIPEDA, PCI DSS, IRDAI, and 50+ regulations — accelerating compliance readiness and simplifying audits across diverse geographies.
Key Capabilities
Why do
customers
choose
Mage Data?

Mage Data is the highest ranked vendor over the past 12 months for "Test Data Management" and "Data Masking & Synthetic Data"
A Unified Platform
- Unified visibility for all enterprise data assets
- Integrated data discovery, classification, masking, db activity monitoring and firewall
- Easy adoption via conversational UI
Simplifying Compliance
- Automated data classification and taxonomy mapping
- Instant alignment with global regulatory mandates
- Streamlined operations for audit readiness
Time to Value
- Go-live in days instead of months
- Pre-built policies and discovery rules
- Immediate results for data protection goals
Experience
- Highest-ranked solution on Gartner Peer Insights
- Proven across global industries and use cases
- Built on verified enterprise customer feedback
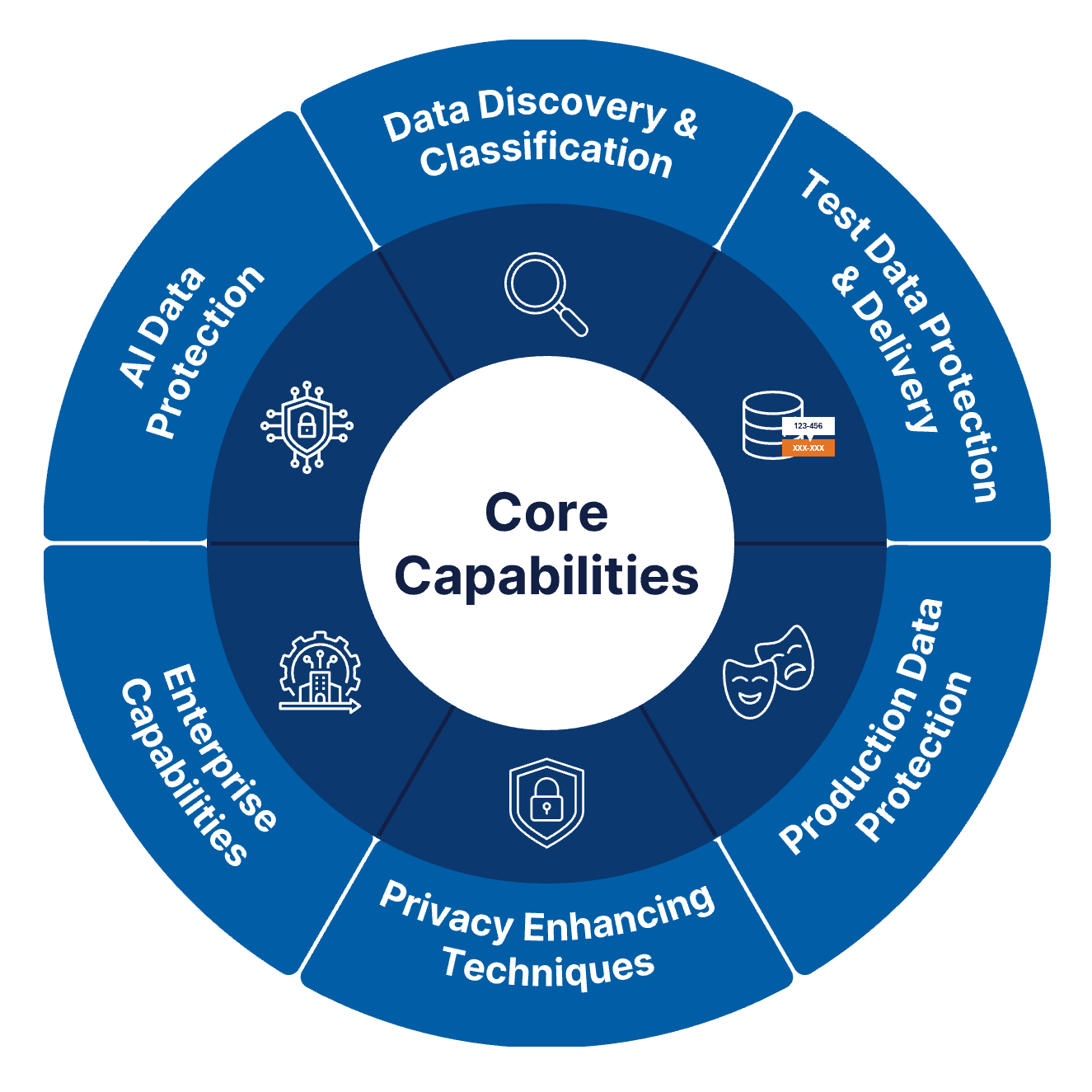
A true single pane of glass
Everything You Need.
Nothing Bolted On.
One Platform.
Every capability is natively built — no need to stitch together multiple applications or disjointed tools. One platform, one policy engine, one unified experience.
-
Natively Built Features
Not assembled rapidly from acquisitions. Built purposefully from the ground up for seamless interaction.
-
Single Policy Engine
Define rules once, apply broadly across production, test, and AI boundaries directly
Global Reach
Trusted Across 20+ Countries & Every Major Regulation
Protecting sensitive data for Global 2000 enterprises across diverse industries and geographies
Some of the Industries We Serve
Industry-agnostic and fully configurable to meet the unique data security needs of any organization
Some of the Regulations We Help Comply With












Pre-built policies for every major regulation — fully configurable to your unique business logic and compliance needs
Connectors & Integrations
Any Datastore. One Data Security Fabric.
28+ connectors supporting 100+ integrations across cloud, on-premises, and hybrid environments
















































































































































What Our Customers Say

Anonymous reviews from verified customers
"Artificial intelligence to uncover data in the most complex of locations"
"Mage Data helps the organization uncover hidden sensitive data locations within the organization with its Sensitive Data Discovery module. This type of discovery is unique to the application, using AI to find data in complex locations. It also maintains compliance with popular data classifications and global privacy regulations, including GDPR, CCPA, and HIPAA. It is an overall recommended Dynamic Data Masking application for the company."
Project Manager, Product Management
Healthcare
Size: 10B‑30B USD
"Offers Superior Features And Support"
"The Mage Data Platform provides all the necessary features for our organization while constantly evolving to meet new needs. The team provides exceptional support throughout the process, ensuring we maximize the software's capabilities. It offers excellent value, delivering high-end services and robust features at a highly competitive price point."
Senior Manager, Data and Analytics
Miscellaneous
Size: 10B - 30B USD
"Dynamic Data Masking has met all of our expectations"
"I like this tool because with its secure anonymization technologies, performance and efficiency are not compromised. It works fast, takes little time to run, and uses minimal system resources. It cleans copies of our production data for testing and development, fully eliminating unnecessary data. Our main motivation was to achieve Dynamic Data Masking and data protection, and DDM has perfectly met those needs. After looking at a few different options, DDM is the best."
IT Domain Manager, Security & Risk Management
Healthcare
Size: 30B+ USD
"Completes Database Masking Workloads Four Times Faster"
"Mage Data Platform's R24 release represents a transformational upgrade in database security. The shift to Docker containerization has dramatically improved deployment efficiency, while performance is exceptional—completing workloads in roughly 25% of the time compared to previous versions. With enhanced APIs for seamless automation and improved usability for static masking, the combination of reliability and speed makes this an outstanding solution for managing complex database environments."
Manager, IT Security and Risk Management
Education
Size: Gov't/PS/ED 5,000 - 50,000 Employees
"Really helpful in protecting most sensitive data elements"
"Static Data Masking is a great technique that provides the flexibility to encrypt data and protect it from attacks and threats. It features various anonymization techniques that safeguard data in non-production environments across applications and third parties like Big Data, Hive, and Oracle. It protects data at enterprise and database layers on any cloud platform. This provides a complete security solution with proper masking techniques to protect sensitive elements."
Decision Analyst, Data and Analytics
Healthcare
Size: 1B‑3B USD
Ready to See the Platform in Action?
Book a personalized demo and discover how Mage Data can simplify compliance, accelerate AI adoption, and transform test data management
